Back to: COMPUTER SCIENCE SS1
Welcome to class!
In today’s class, we will be talking about the abuse of the internet. Enjoy the class!
Abuse of the Internet
Internet abuse refers to improper use of the internet and may include:
-
Computer crime or cybercrime:
It is any crime that involves a computer and a network. Use of computers for criminal activity. New technologies create new criminal opportunities but few new types of crime. What distinguishes cybercrime from traditional criminal activity? One difference is the use of the digital computer, but technology alone is insufficient for any distinction that might exist between different realms of criminal activity. Criminals do not need a computer to commit fraud, traffic in child pornography and intellectual property, steal an identity, or violate someone’s privacy. All those activities existed before the “cyber” prefix became ubiquitous. Cybercrime, especially involving the Internet, represents an extension of existing criminal behaviour alongside some novel illegal activities.
Most cybercrime is an attack on information about individuals, corporations, or governments. Although the attacks do not take place on a physical body, they do take place on the personal or corporate virtual body, which is the set of informational attributes that define people and institutions on the Internet. In other words, in the digital age, our virtual identities are essential elements of everyday life: we are a bundle of numbers and identifiers in multiple computer databases owned by governments and corporations. Cybercrime highlights the centrality of networked computers in our lives, as well as the fragility of such seemingly solid facts as individual identity.
An important aspect of cybercrime is its nonlocal character: actions can occur in jurisdictions separated by vast distances. This poses severe problems for law enforcement since previously local or even national crimes now require international cooperation. For example, if a person accesses child pornography located on a computer in a country that does not ban child pornography, is that individual committing a crime in a nation where such materials are illegal? Where exactly does cybercrime take place? Cyberspace is simply a richer version of the space where a telephone conversation takes place, somewhere between the two people having the conversation.
As a planet-spanning network, the Internet offers criminals multiple hiding places in the real world as well as in the network itself. However, just as individuals walking on the ground leaving marks that a skilled tracker can follow, cybercriminals leave clues as to their identity and location, despite their best efforts to cover their tracks. To follow such clues across national boundaries, though, international cybercrime treaties must be ratified.
-
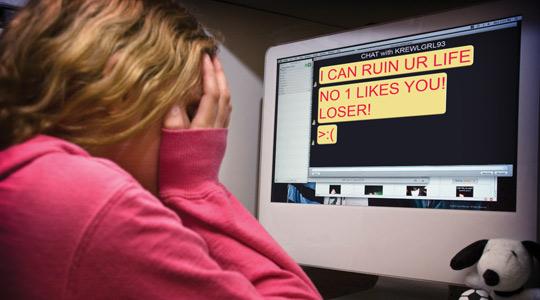
Cyber-bullying:
Use of the internet to bully and intimidate. The use of information technology to repeatedly harm or harass other people in a deliberate manner.
-
Spam (electronic):
Is the use of electronic messaging systems to send unsolicited messages (spam), especially advertising, as well as sending messages repeatedly on the same site. Sending of unwanted advertising messages.
-
Malware:
Software designed to harm a user’s computer, including computer viruses. Malware, short for malicious software, is any software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. Malware is defined by its malicious intent, acting against the requirements of the computer user, and does not include software that causes unintentional harm due to some deficiency.
-
Other ways of abuse include:
- You can get harassing/threatening messages from people or from stalkers.
- It is very easy to find sites that promote hatred, violence, drug, sex, and other things not appropriate for children.
- There is no restriction on marketing products, such as alcohol, tobacco to children on the internet.
- Request for personal information for contests, survey etc. are used in an unauthorized way.
- Pornographic sites are easily found on the internet instead of it being restricted.
- Time wastage
- Hacking
- Posting of fake advertisements of Jibs and products
- Internet scam
- Piracy: Piracy is the act of illegally copying or downloading copyrighted material. People commit piracy because it saves money at their end.
Evaluation
In what form does internet abuse occur?
In our next class, we will be talking about Computer Ethics. We hope you enjoyed the class.
Should you have any further question, feel free to ask in the comment section below and trust us to respond as soon as possible.